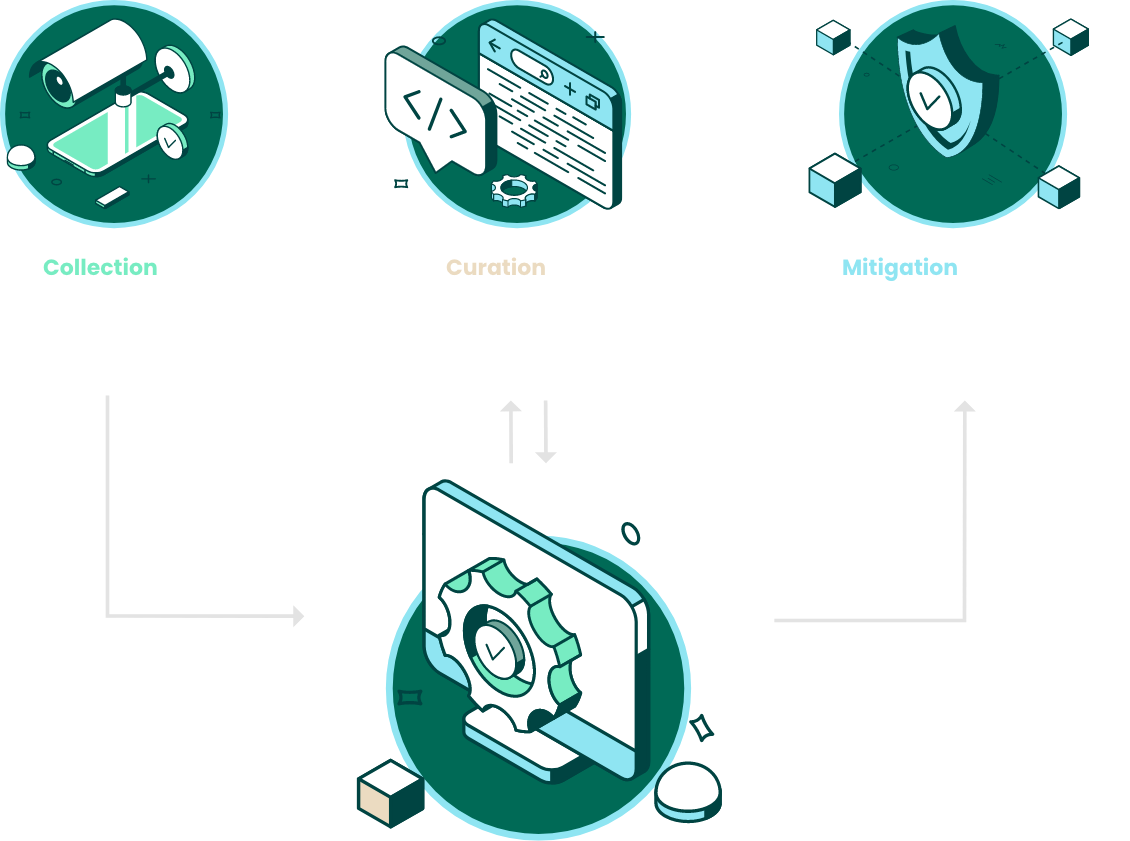
How It Works
The PhishLabs Platform is the foundation of our Digital Risk Protection solution. Developed over a decade in partnership with the world’s most targeted brands, the PhishLabs Platform delivers comprehensive collection, expert curation, and complete mitigation of digital risks, such as brand impersonation, data leakage, social media threats, and account takeover in one complete solution.
Gain Visibility into External Threats
Brand impersonation, data leakage, and other external threats can happen anywhere online. Without extensive visibility across digital channels, these threats can easily go undetected and cause substantial harm.
Our Digital Risk Protection solution, powered by the PhishLabs Platform, delivers comprehensive visibility by collecting massive amounts of data across the surface, deep, and dark web. We monitor thousands of social media sources and ingest data from hundreds of public and private data feeds. We also integrate data from client-specific sources such as referrer logs and any third-party feeds.
This data is aggregated and processed at scale, incorporating automated crawling, parsing, anti-evasion, and pivoting processes to generate intelligence. The intelligence is enriched by our experts, who use advanced sourcing techniques to supplement the platform.
Machine and Human Collection Methods
Web
Surface, Deep, Dark Web, Mobile App Stores
Data Feeds
URLs, Passive DNS, SSL Certs, Email and SMS Spam, Malware

Social
Social Networks, Paste Sites, Gripe Sites, Blogs

Client Sources
3rd Party Feeds, Referrer Logs, Abuse Reports, Web Beacon
Comprehensive Intelligence Sourcing

Parsing
Flexible Parsing Automates Data Ingestion Across Sources

Anti-evasion
Anti-Evasion Techniques Detect Hidden Malicious Content

Crawling
Advanced Crawling Technology Captures Web Data

Pivoting
Pivoting Processes Identify Related Threat Infrastructure
Reduce Noise, Find Threats

The sheer volume of data on the web is overwhelming and growing exponentially. Intelligence tools built to monitor for online threats burden teams with additional responsibilities, divert resources from high-value initiatives, and generate too much noise. False positives are more common than real threats, creating an inefficient process where analysts are forced to churn through haystacks of low fidelity hits.
Our Digital Risk Protection solution removes this burden by incorporating advanced automated analysis with expert vetting. This eliminates false positives and delivers curated intelligence that is ready for action.
With automated analysis and risk-scoring algorithms, the platform processes massive amounts of collected intelligence in near real-time to find references to client assets. PhishLabs analysts then review, validate, and categorize the machine-filtered results to produce expert-vetted, curated intelligence. The platform is constantly tuned by our experts, ensuring collection and analysis processes align with current and future needs of each client.
Our curation process ensures that accurate, high fidelity intelligence is delivered. It minimizes the need for additional analysis and review prior to taking action. In doing so, the platform streamlines the response process and reduces the lifespan of threats while reducing security team workloads.
Address Threats Quickly and Completely
Successful Digital Risk Protection requires a comprehensive mitigation strategy that can rapidly and completely protect against online threats. Partial mitigation strategies, such as integrating threat indicators into internal security controls, are not enough to prevent harm to brands, customers, and employees.
PhishLabs delivers a complete mitigation strategy through our extensive global takedown network, browser-blocking, and automated integrations with internal controls.
Instead of relying primarily on automated form submissions and emails, the PhishLabs Platform connects directly to service providers via proprietary Killswitches and Takedown APIs. This delivers the fastest and most successful takedown capability in the industry. By combining takedown, browser-blocking, and integration with internal security controls, PhishLabs ensures threats are quickly and completely mitigated.

Global Takedown Network
Killswitch Integrations, Takedown APIs, Strategic Relationships, Browser-blocking, DMCA Takedowns

API Integrations
APIs, SIEMs, SOARs, TIPs, FWs, IDPS

Client Web App
Executive Dashboard, Incident Management, Intuitive Workflows, Reporting and Analytics

Reporting APIs
Threat Intelligence Indicators, Incident Data Reporting, Incident Creation
Centers of Excellence
Different threats demand different approaches. For example, look-alike domains and fake social accounts are two very different problems that require distinct collection, curation, and mitigation. Using the same technology and operations for both leads to neither being addressed well.
That’s why PhishLabs established Centers of Excellence that bring a critical mass of threat-specific technology and operations. Our Centers of Excellence drive our collection efforts to source intelligence that delivers better visibility into threats early in the attack process. Collected intelligence is curated by specialists using threat-specific processes and context. Mitigation is enhanced with handling procedures and workflows purposefully designed to mitigate specific threat types as quickly and thoroughly as possible.
As a result, our Centers of Excellence deliver unparalleled threat detection and mitigation.
Explore the PhishLabs Digital Risk Protection Platform Solutions
Brand Protection
Continuously collects massive amounts of data from the surface web, deep web, dark web, and social media to identify content containing brand keywords and variations.
Account Takeover Protection
Provides access to an extensive global network of provider relationships that can mitigate attacks, disrupt phishing campaign infrastructures, and rapidly take down phishing sites to reduce risk of account compromise.
External Data Leaks
Provides 24 × 7 visibility across a vast stretch of digital channels to proactively detect data leaks, maintain ongoing monitoring of data claimed by threat actors, and quickly take down leaks posted to open web and social media.
Security Awareness Training
Delivers targeted, engaging training with a practical, people-centric approach with modules and simulations designed to reduce risk and help create a strong human line of defense against cyberattacks.
Social Media Protection
Gathers data from thousands of social media sites, categorizes them, and adds context to threats with finely tuned, automated risk analysis combined with expert review.